138/69 Tuesday, March 10, 2026
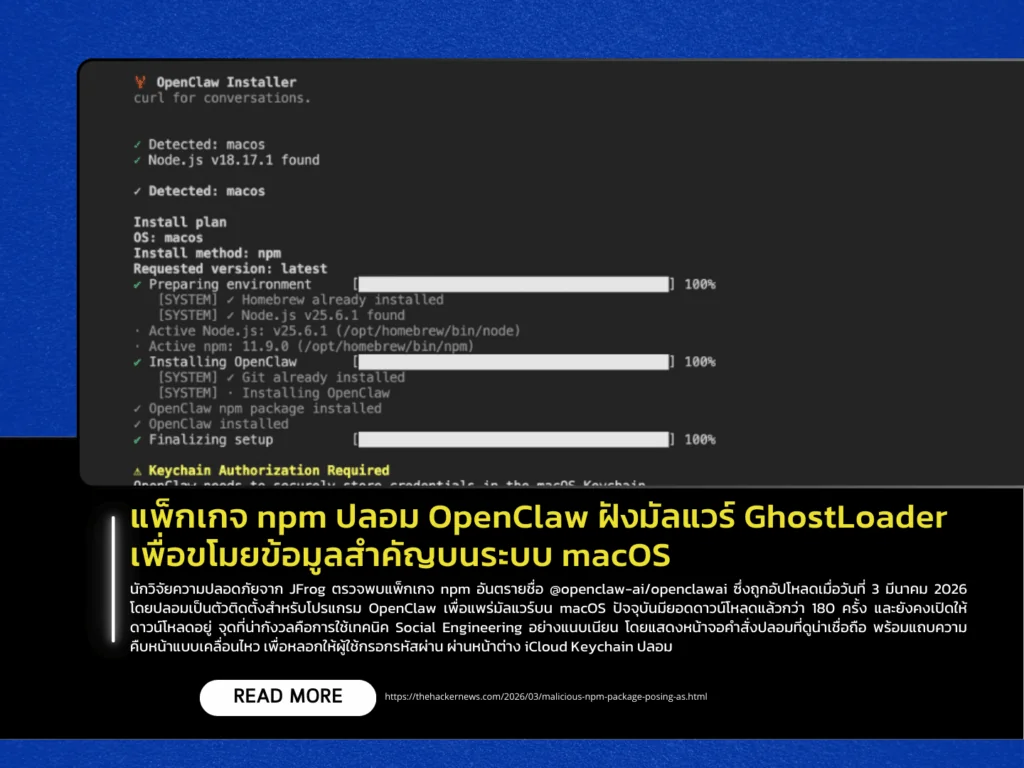
Security researchers from JFrog have discovered a malicious npm package named @openclaw-ai/openclawai, uploaded on March 3, 2026. The package impersonates an installer for the OpenClaw application and is designed to spread malware on macOS systems. The package has already been downloaded more than 180 times and remains available for download. Researchers noted that the attack uses sophisticated social engineering techniques, including a convincing fake command-line interface with animated progress indicators to deceive users into entering their passwords through a fraudulent iCloud Keychain prompt.
The embedded malware, which identifies itself as GhostLoader, executes through a postinstall hook and launches an initial-stage script. It then attempts to obtain Full Disk Access using an AppleScript dialog, allowing it to access protected system data. In later stages, the payload is capable of stealing sensitive information such as the Apple Keychain database, browser data (including cookies, passwords, and payment card information), SSH keys, and credentials for cloud services including Amazon Web Services, Microsoft Azure, Google Cloud Platform, and GitHub, as well as conversation histories from iMessage.
In addition, the malware includes Remote Access Trojan (RAT) capabilities, enabling attackers to remotely control infected systems, configure a SOCKS5 proxy, and perform browser session cloning, allowing attackers to reuse active browser sessions without knowing the user’s password. The malware also maintains persistence by continuously monitoring the clipboard every three seconds to search for sensitive data such as private keys, cryptocurrency wallet information, and API keys.
This incident highlights the growing risks posed by malicious npm packages that combine social engineering, data theft, and remote system control within a single package. Users are strongly advised to carefully verify the origin and legitimacy of packages before granting system permissions or entering sensitive credentials.
Source https://thehackernews.com/2026/03/malicious-npm-package-posing-as.html
