212/69 Monday, April 20, 2026
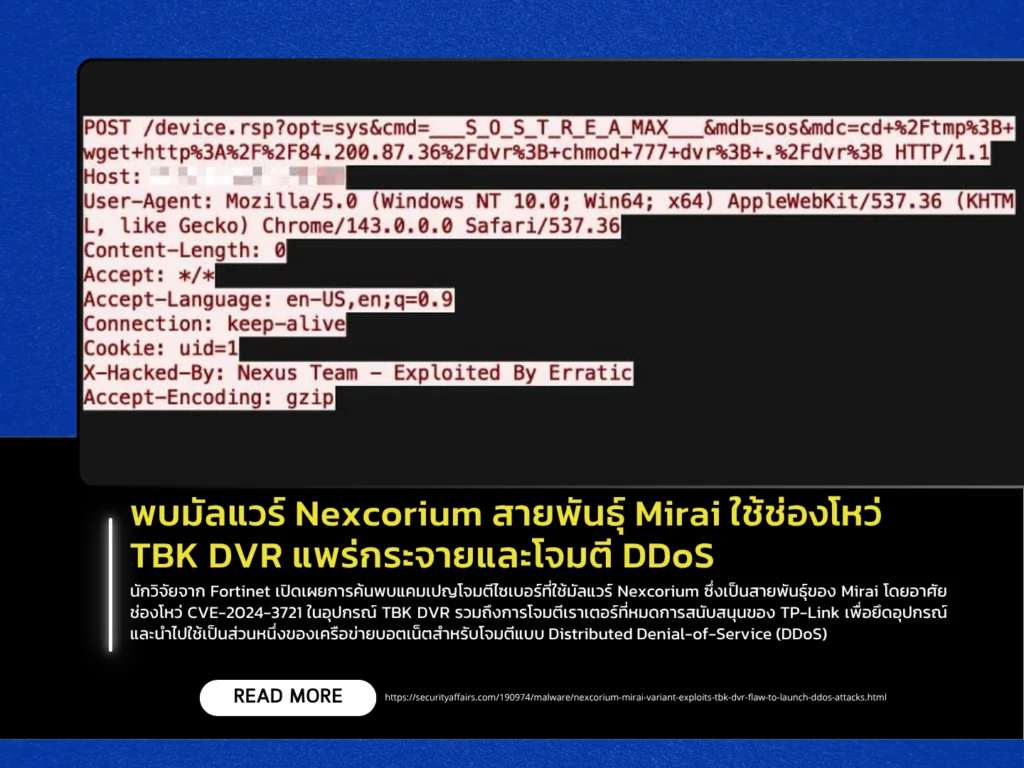
Researchers from Fortinet have uncovered a cyberattack campaign leveraging Nexcorium, a variant of the Mirai malware. The campaign exploits CVE-2024-3721, a command injection vulnerability in TBK DVR devices, along with attacks targeting end-of-life TP-Link routers. These compromised devices are then recruited into botnets used for Distributed Denial-of-Service (DDoS) attacks. The vulnerability allows attackers to execute arbitrary commands remotely and take full control of affected devices.
The attack typically begins with exploitation of the vulnerability to download and deploy malware onto targeted devices. Nexcorium supports multiple architectures, including ARM, MIPS, and x86-64, enabling widespread propagation. Like Mirai, it connects to command-and-control (C2) servers to receive attack instructions and can launch various types of DDoS attacks, such as UDP and TCP floods. It also includes persistence mechanisms and evasion techniques to remain undetected within infected systems.
In addition, the malware can exploit other vulnerabilities and use brute-force techniques to expand its reach across more devices. This highlights a growing trend of attackers targeting unpatched IoT devices and outdated systems. Experts strongly recommend applying security patches, changing default passwords, and restricting external access to devices to prevent compromise and participation in large-scale botnet attacks.
