224/69 Friday, April 24, 2026
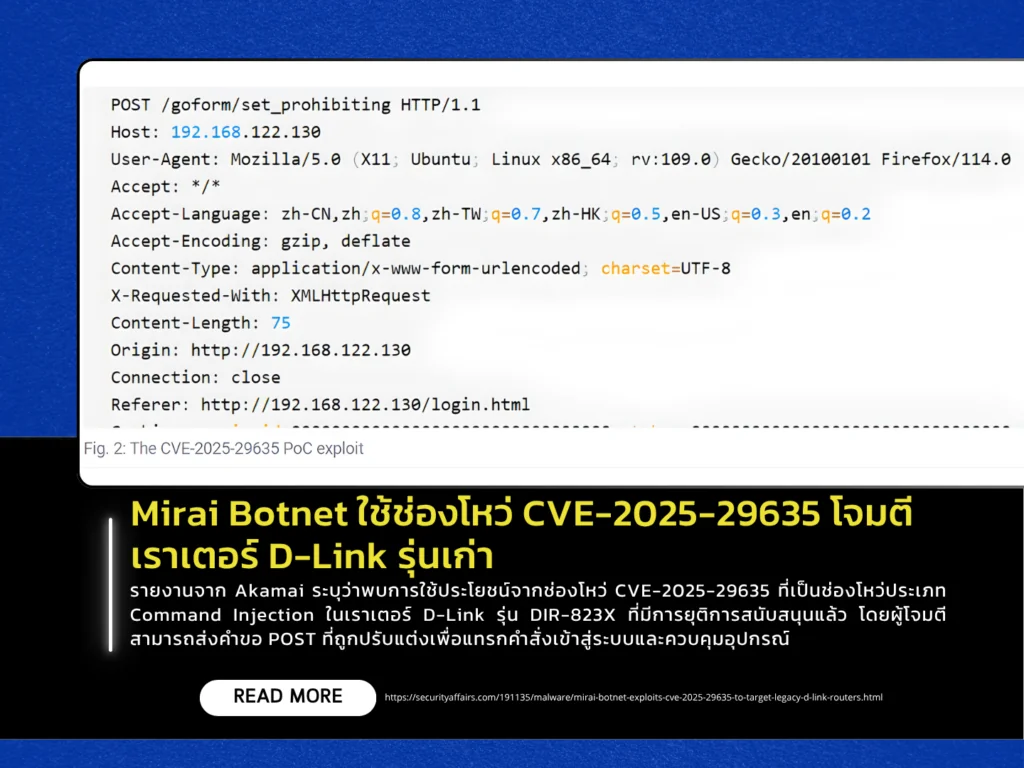
A report from Akamai reveals active exploitation of CVE-2025-29635, a command injection vulnerability affecting end-of-life D-Link DIR-823X routers. Attackers can send specially crafted POST requests to inject commands into the system and gain control of the device. The flaw stems from improper input validation, allowing user-controlled data to be passed directly into the system() function for execution. Exploitation activity was observed shortly after the vulnerability and its Proof-of-Concept (PoC) were publicly disclosed.
The vulnerability is being used to deploy Mirai-based malware. Attackers download payloads from external infrastructure and install them on compromised devices. One observed variant, “tuxnokill,” supports multiple architectures, uses XOR-based obfuscation, and connects to command-and-control (C2) servers to launch Distributed Denial-of-Service (DDoS) attacks. Researchers also noted that attackers are combining this exploit with other known vulnerabilities, such as CVE-2023-1389 in TP-Link devices and additional flaws in ZTE equipment, to expand their reach.
This incident highlights a growing trend of attackers leveraging older vulnerabilities with publicly available PoCs, as they are easier and faster to exploit—especially on unpatched or unsupported devices. Experts recommend that organizations and users regularly audit network devices, update firmware where possible, replace outdated hardware, and closely monitor vulnerability disclosures to prevent devices from being compromised and recruited into large-scale botnets.
