271/68 Tuesday, July 29, 2025
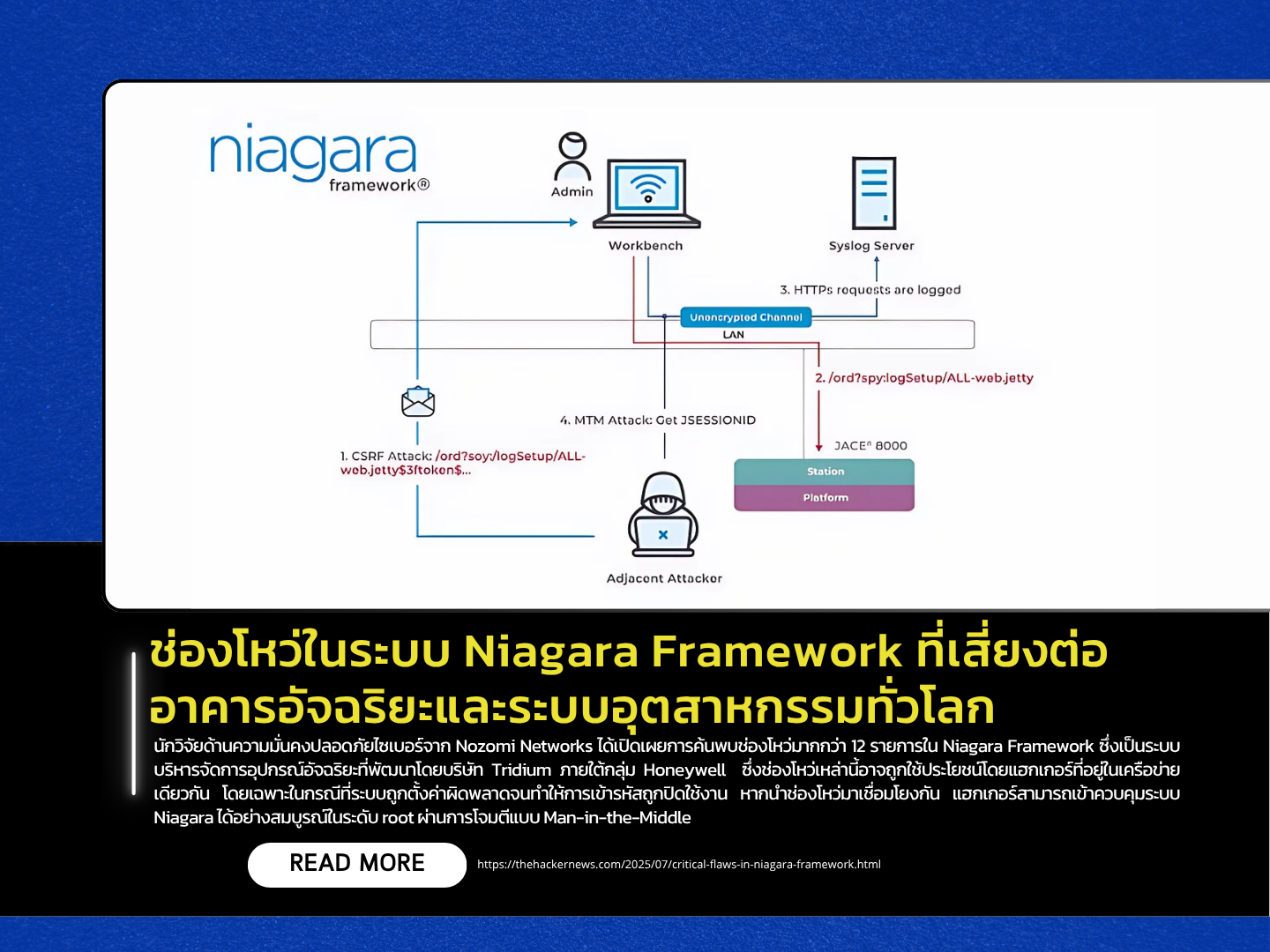
Cybersecurity researchers from Nozomi Networks have disclosed the discovery of more than 12 vulnerabilities in the Niagara Framework, an intelligent device management system developed by Tridium, a subsidiary of Honeywell. These vulnerabilities could be exploited by attackers within the same network, especially when misconfigurations leave encryption disabled. When chained together, the flaws could allow attackers to gain full root-level control of Niagara systems through Man-in-the-Middle (MitM) attacks — potentially impacting key control systems such as lighting, HVAC, energy, and security in smart buildings and industrial infrastructure.
According to the report, at least six of the most severe vulnerabilities received a CVSS score of 9.8, including:
- Improper authorization flaws (CVE-2025-3936, CVE-2025-3944),
- Incomplete encryption (CVE-2025-3938),
- and Remote code execution via external command invocation (CVE-2025-3945).
Researchers demonstrated a chained exploit combining CVE-2025-3943 and CVE-2025-3944 to escalate privileges to administrator level, then extract TLS secret keys to perform Adversary-in-the-Middle attacks — achieving complete control over both the Niagara Platform and Station components. All reported vulnerabilities have been patched in the following updated versions: Niagara 4.14.2u2, 4.15u1, and 4.10u.11. Organizations are advised to apply these patches and configure their systems according to Tridium’s hardening guidelines.
This disclosure comes alongside reports of other industrial vulnerabilities, including flaws in the P-Net C library used in PROFINET devices, which could lead to infinite CPU loops (100% CPU usage) or buffer overflows. Additional vulnerabilities were identified in:
- PowerMonitor 1000 by Rockwell Automation,
- IB-MCT001 cameras by Inaba Denki, and
- ctrlX CORE controllers by Bosch.
All could be leveraged for unauthorized access, data exfiltration, or remote system control. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned that these flaws may lead to password theft, data tampering or deletion, and malicious control over industrial devices.
Source https://thehackernews.com/2025/07/critical-flaws-in-niagara-framework.html
