137/69 Tuesday, March 10, 2026
A critical security vulnerability has been discovered in Nginx UI, tracked as CVE-2026-27944 with a CVSS score of 9.8. The flaw could allow attackers to download and decrypt server backup files without authentication, potentially exposing sensitive information such as system configurations, credentials, and encryption keys-particularly if the management interface is accessible from the public internet.
According to the report, the issue originates from the /api/backup endpoint, which can be accessed without authentication. This allows attackers to directly request system backup files. Additionally, the server exposes the AES-256 encryption key and Initialization Vector (IV) through the HTTP header X-Backup-Security, enabling attackers to immediately decrypt the downloaded backup data. The backup files may contain highly sensitive information, including user account data, session tokens, private SSL keys, Nginx configuration files, databases, and other system resources. Exposure of this information could lead to full system compromise or unauthorized access to an organization’s infrastructure.
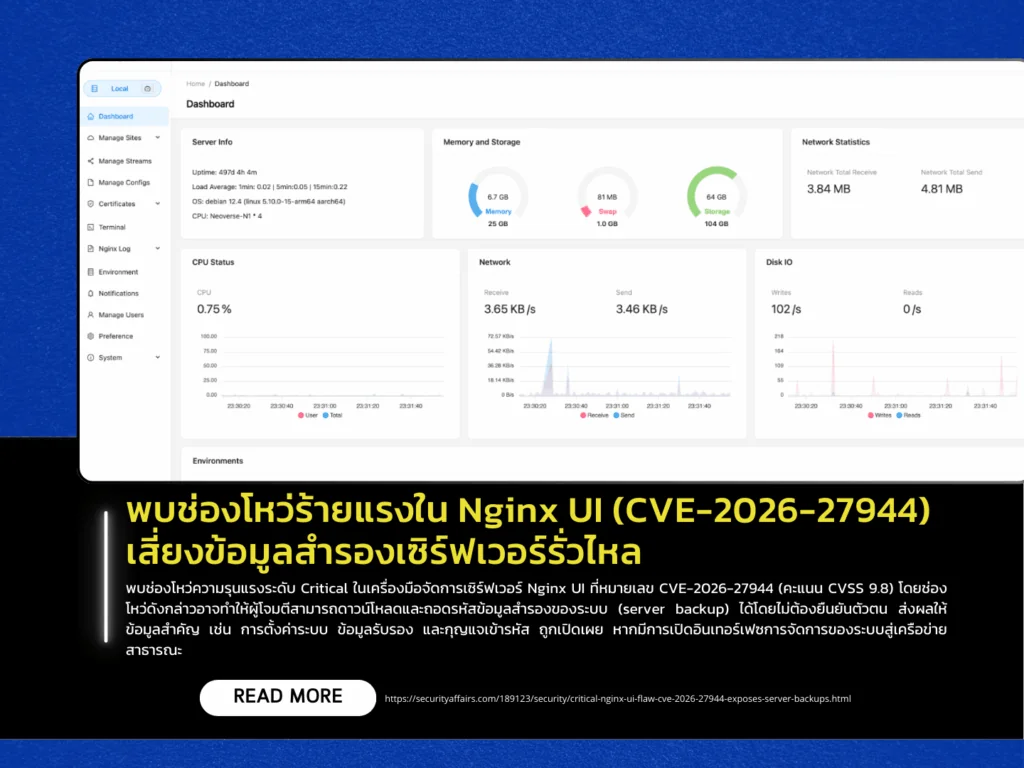
Nginx UI is a web-based dashboard designed to manage Nginx servers, allowing administrators to configure settings, monitor performance, and control server operations without editing configuration files through the command line. However, exposing such management interfaces directly to the public internet significantly increases security risks. Security experts recommend restricting access to internal networks or VPN-only connections, implementing additional protections such as IP allowlisting, multi-factor authentication (MFA), and network segmentation, and regularly auditing APIs and system endpoints. These measures can help mitigate design flaws that might otherwise lead to severe security and data exposure incidents within enterprise environments.
