150/69 Monday, March 16, 2026
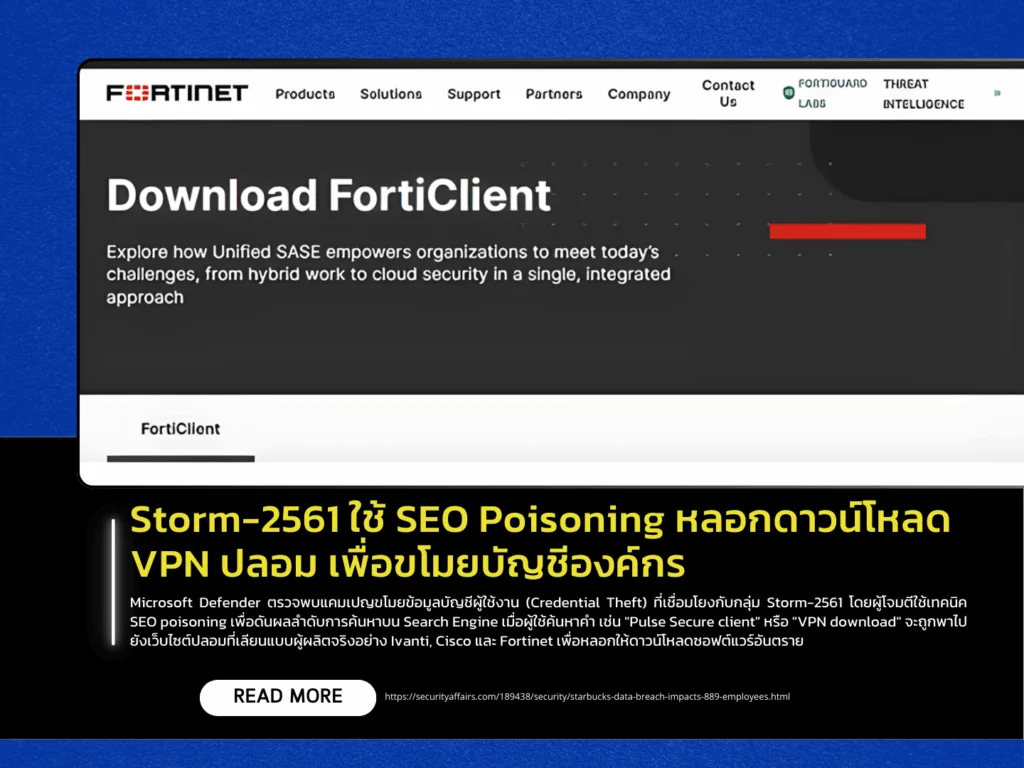
Researchers from Microsoft Defender have identified a credential-theft campaign linked to the threat actor Storm‑2561. In this campaign, attackers use SEO poisoning to manipulate search engine rankings. When users search for terms such as “Pulse Secure client” or “VPN download,” they are redirected to fake websites impersonating legitimate vendors including Ivanti, Cisco, and Fortinet, where they are tricked into downloading malicious software.
After victims download a ZIP file hosted on GitHub and execute a modified MSI installer, the malware deploys files onto the system and uses DLL sideloading to load the Hyrax infostealer. This malware can steal VPN login credentials and extract connection details from the connectionstore.dat file. It also establishes persistence by creating a RunOnce registry entry, enabling the malware to execute automatically each time the system restarts. To evade detection, the malicious installer was initially signed with a digital certificate, which was later revoked after the activity was discovered.
Microsoft also highlighted another key tactic in the campaign known as post-theft redirection, designed to conceal the compromise after credentials have already been stolen. Once the malware completes data exfiltration, it displays a convincing error message and advises the user to download the VPN client from the official website instead. If the victim subsequently installs the legitimate software successfully, the earlier incident appears to be nothing more than a technical error, preventing the user from realizing that sensitive credentials have already been transmitted to the attackers’ command-and-control (C2) servers.
