151/69 Tuesday, March 17, 2026
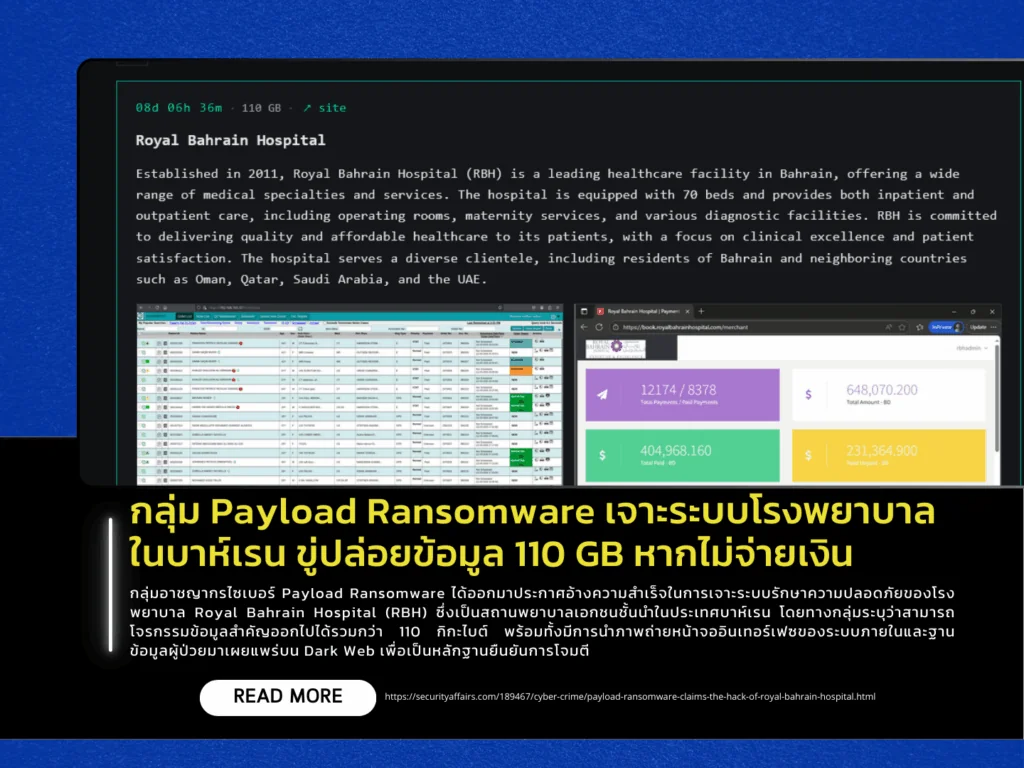
The cybercriminal group Payload Ransomware has claimed responsibility for breaching the systems of Royal Bahrain Hospital (RBH), a leading private healthcare provider in Bahrain. The group alleges that it has exfiltrated more than 110 GB of sensitive data and has published screenshots of internal system interfaces and patient databases on the dark web as proof of the attack. The attackers have issued an ultimatum, threatening to publicly release the stolen data unless a ransom is paid by March 23.
Royal Bahrain Hospital, established in 2011, is a 70-bed medical facility offering both inpatient and outpatient services, including surgical care and advanced diagnostic centers. It serves a large number of patients not only from Bahrain but also from neighboring countries such as Oman, Qatar, Saudi Arabia, and the United Arab Emirates. The breach has therefore raised significant concerns about the privacy of sensitive patient data, including personal information and medical records, across the region.
From a technical perspective, Payload is a relatively new ransomware group that employs a double-extortion model—encrypting systems while simultaneously stealing data to increase pressure on victims. The malware uses advanced encryption algorithms such as ChaCha20 and Curve25519 for key exchange. It also includes capabilities to delete backups and disable security software, hindering recovery efforts. The group is believed to operate under a Ransomware-as-a-Service (RaaS) model, with a structured division of roles for malware deployment and ransom negotiation.
