169/69 Wednesday, March 25, 2026
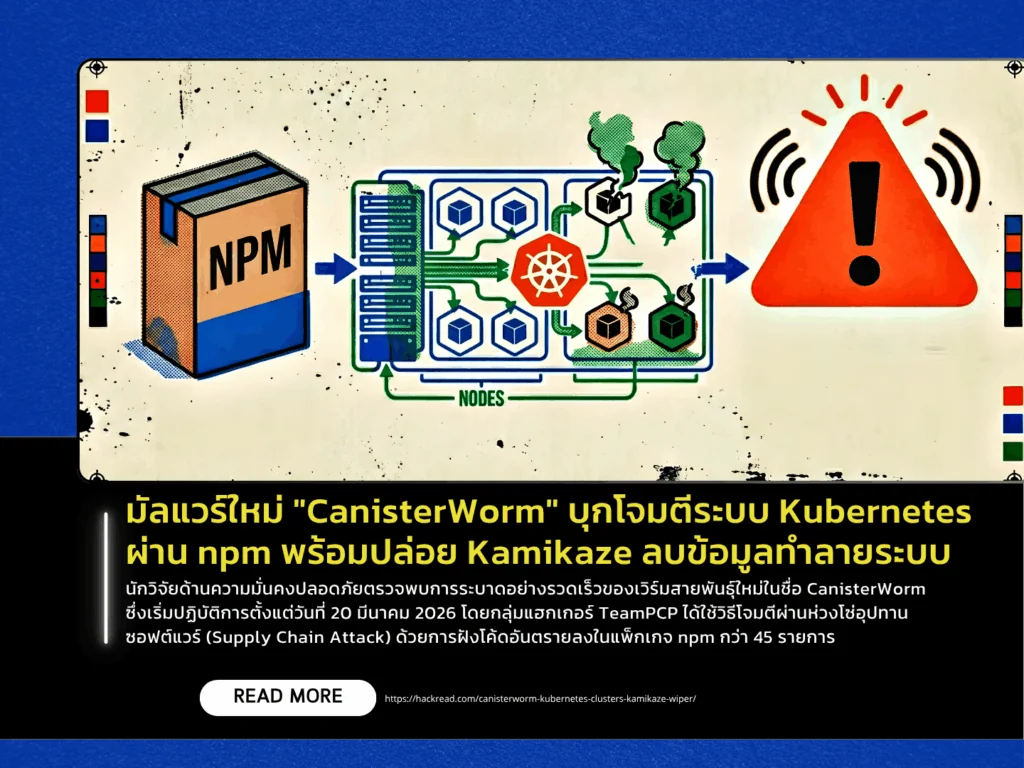
Security researchers have identified a rapidly spreading new worm named CanisterWorm, active since March 20, 2026. The campaign is attributed to the hacker group TeamPCP, which leveraged a software supply chain attack by embedding malicious code into more than 45 npm packages. The compromise is believed to stem from stolen maintainer credentials, potentially linked to a prior data leak involving the Trivy vulnerability scanning tool. The malware demonstrates highly aggressive propagation capabilities, spreading across systems within seconds by stealing SSH keys and harvesting authentication tokens to compromise additional software accounts.
A key technical feature that makes mitigation difficult is its use of Blockchain Canisters on the Internet Computer Protocol (ICP) as its command-and-control (C2) infrastructure, instead of traditional centralized servers. Due to the decentralized nature of blockchain, taking down the C2 infrastructure is significantly more challenging. Notably, CanisterWorm exhibits targeted behavior: if it detects that it is running within a Kubernetes environment located in Iran (Asia/Tehran timezone), it escalates into a Kamikaze Wiper. In this mode, it deploys a DaemonSet to execute across all nodes, wiping data and destroying systems immediately. Outside of this region, the malware operates as a backdoor, focusing on data exfiltration and espionage.
To mitigate the threat, developers and system administrators are strongly advised to conduct thorough inspections of their network environments and Kubernetes clusters, particularly looking for suspicious services named pgmon or pgmonitor, which the malware uses for disguise. Organizations should also review the use of authentication tokens and enforce strict access controls. Given its ability to spread beyond cloud environments into internal infrastructure, CanisterWorm poses a significant and evolving threat that requires immediate attention.
Source https://hackread.com/canisterworm-kubernetes-clusters-kamikaze-wiper/
