254/69 Monday, May 11, 2026
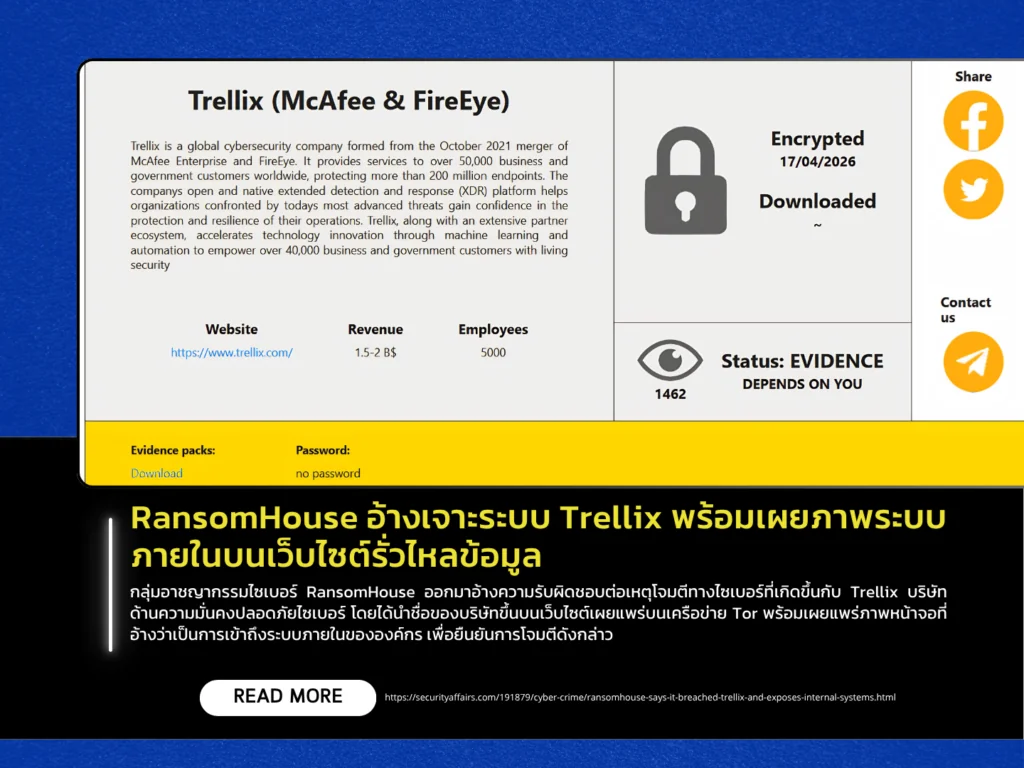
The cybercriminal group RansomHouse has claimed responsibility for a cyberattack targeting Trellix, listing the company on its Tor-based leak site and publishing screenshots allegedly showing access to the organization’s internal systems as proof of compromise. Earlier in May, Trellix disclosed that it had detected unauthorized access affecting part of its source code repository infrastructure. The company stated that it immediately launched an investigation with the assistance of digital forensics experts and notified relevant law enforcement authorities. Trellix also emphasized that, at this stage, there is no evidence indicating that its source code distribution processes or products were compromised, nor that the source code has been used in subsequent attacks.
Incidents of this nature can pose significant cybersecurity risks because unauthorized access to internal source code repositories may expose sensitive information such as system architecture, API structures, access credentials, or undisclosed vulnerabilities that could later be weaponized to develop further attacks. In addition, such breaches raise concerns regarding potential supply chain risks if malicious code were to be inserted or modified before software distribution to customers. However, no additional details have yet been disclosed regarding the intrusion method or how long the attackers maintained access to the environment.
RansomHouse first emerged in late 2021 and initially distinguished itself from traditional ransomware groups by focusing primarily on data theft and extortion rather than encrypting victims’ systems. The group has since claimed attacks against numerous major organizations worldwide across the technology, healthcare, government, and critical infrastructure sectors. Its operations commonly involve exploiting internet-exposed services, weak passwords, phishing campaigns, and vulnerable remote access systems to gain unauthorized access to victim networks.
